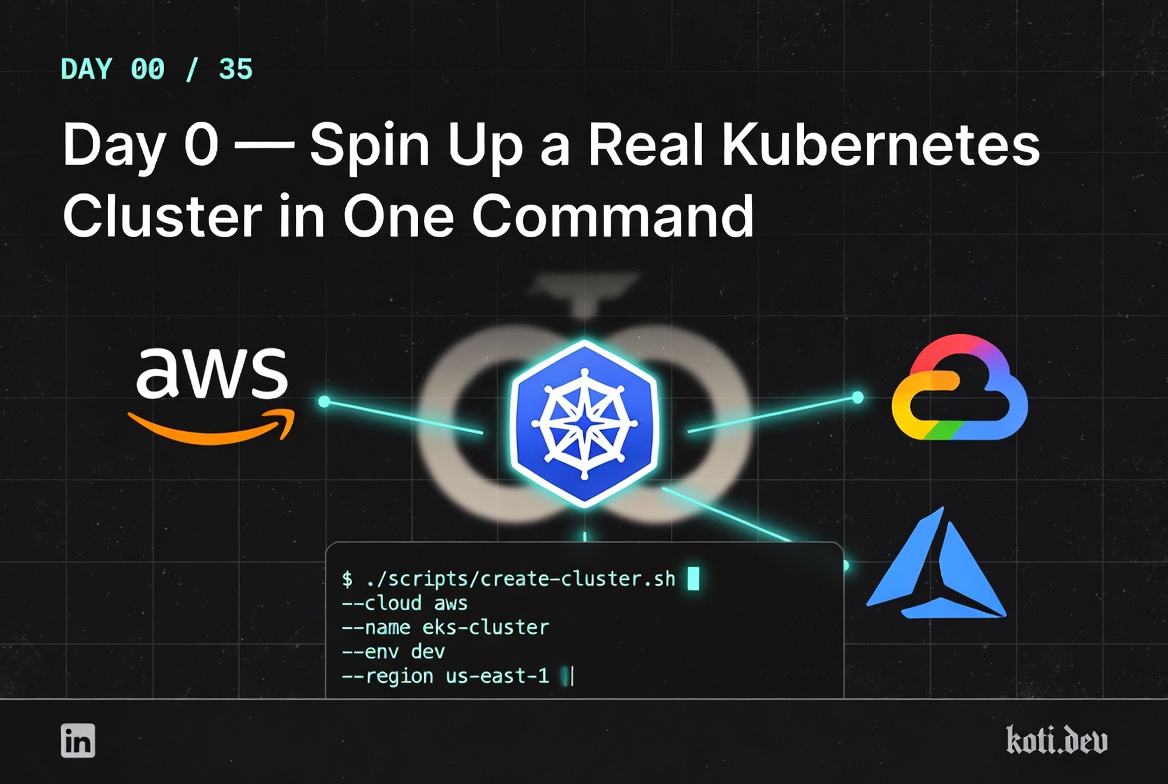
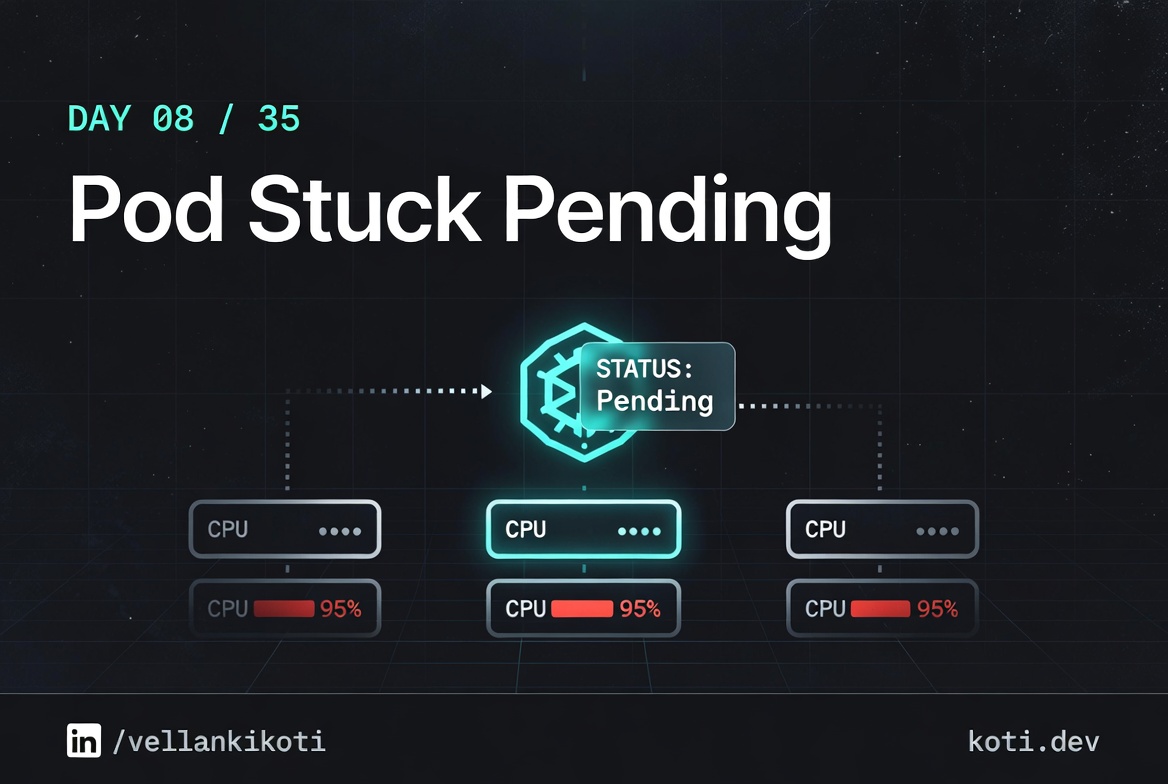
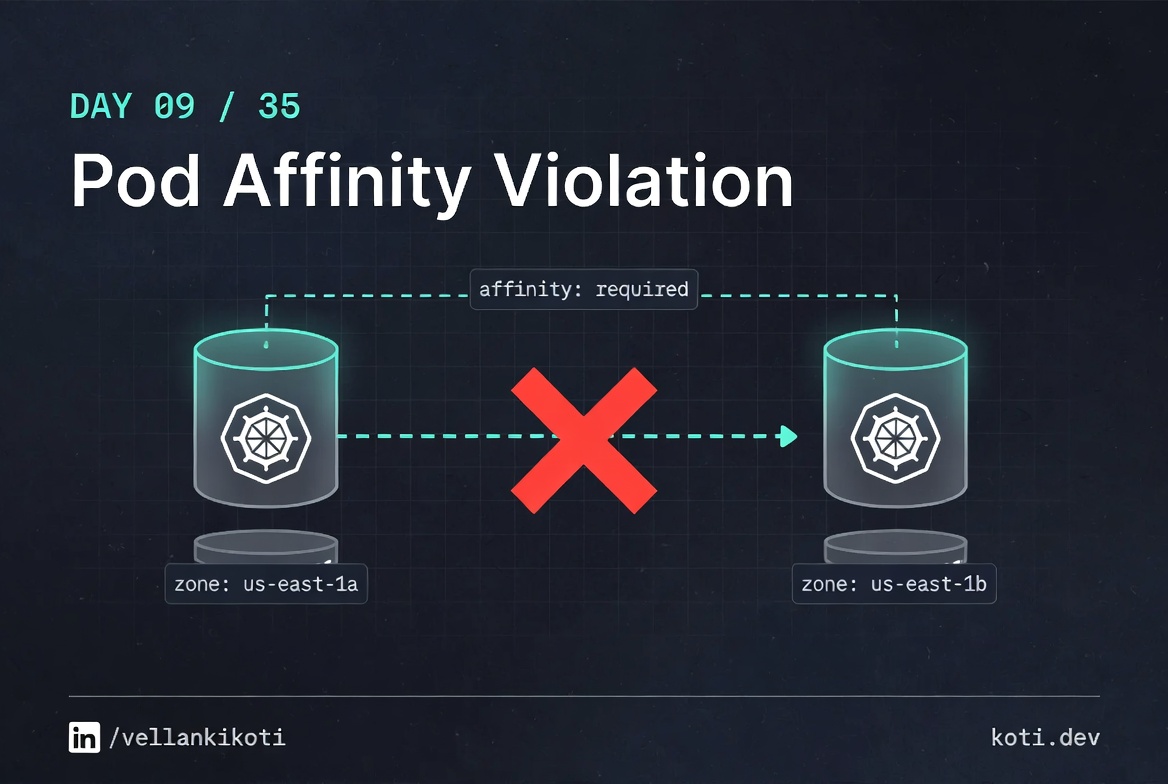
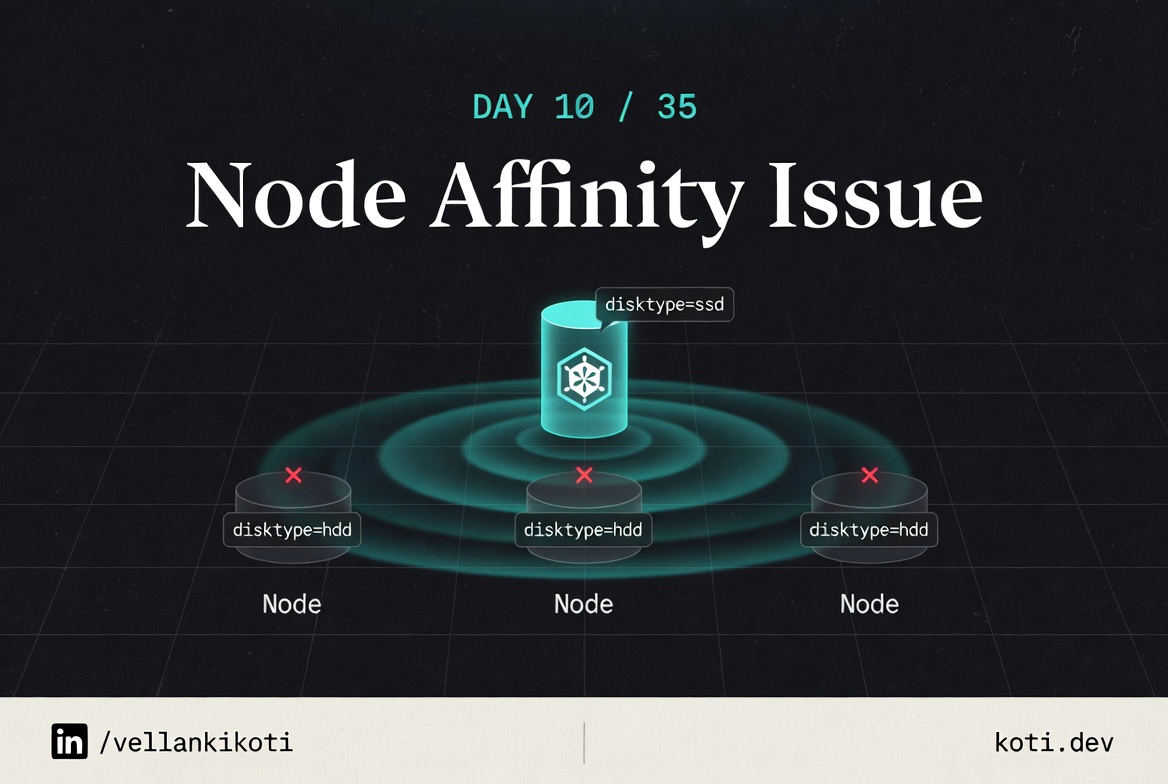
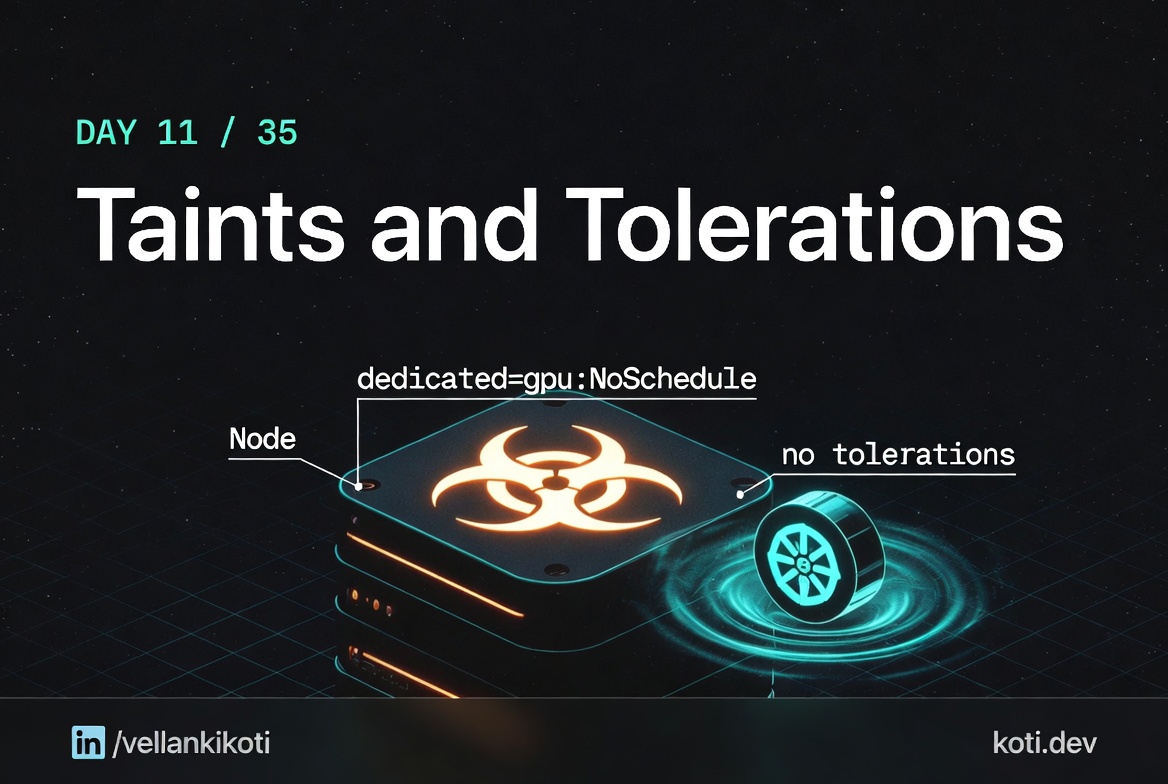
The 35-part Kubernetes series
32 / 35 publishedview all →Talk · 2025
PyCon UK
Talk · 2025
PyCon Spain
Talk · 2025
PyCon Hong Kong
Collabnix
ACTIVE ORGANIZER· 13,000+ MEMBERS
India CodeWeekend
ORGANIZER· 10,000+ MEMBERS
Open Source Meetups Bengaluru
COMMUNITY LEADER· 2,600+ MEMBERS